One of the less common update errors in Ubuntu is 'following signatures couldn't be verified'.
It's more of a warning (the message starts with W, not E). However, it ignores the packages coming from the repository that are impacted by this issue.
The error has several variants, if I can call that. I encountered this one when I was trying to install MATE desktop on Ubuntu,
W: GPG error: http://repo.mate-desktop.org saucy InRelease: The following signatures couldn’t be verified because the public key is not available: NO_PUBKEY 68980A0EA10B4DE8Another variant of this message is about EXPKEYSIG. I encountered this on my DigitalOcean server that comes preconfigured with Ghost.
W: An error occurred during the signature verification. The repository is not updated and the previous index files will be used. GPG error: https://dl.yarnpkg.com/debian stable InRelease: The following signatures were invalid: EXPKEYSIG 23E7166788B63E1E Yarn Packaging [email protected]So, first, let's understand the root cause.
Why do you see this error?
The APT package manager on Ubuntu and Debian-based distributions employs a trust/security mechanism with GPG. Like SSH, GPG also has public-private key pair. The public key is shared and the private key is kept secret.
Every repository, be it from Ubuntu itself or a PPA or a third-party repository, is signed with GPG keys by its developer. When you add a repository to your system, the public GPG key of its developer is added to trusted GPG keys on your system. This ensures that your Linux system trusts the packages coming from the repository.
You can see the GPG keys stored on your system using this command:
apt-key list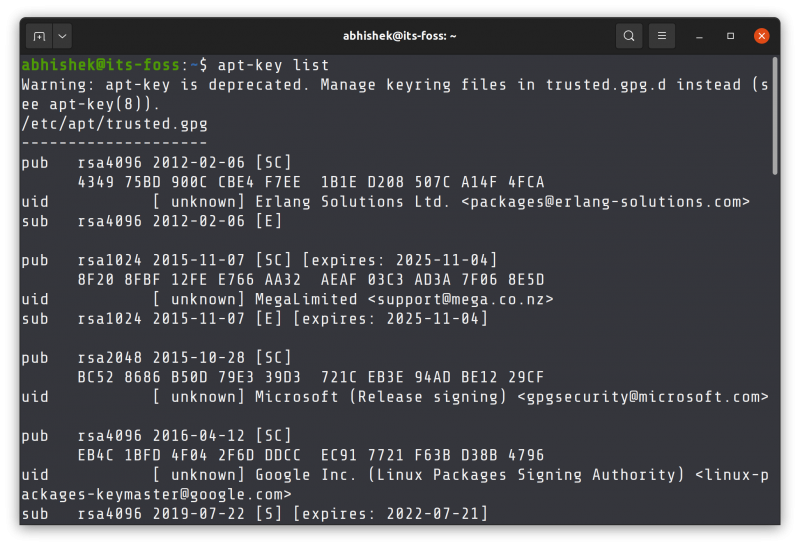
There is a newer mechanism being put in place that recommends putting the keys in /usr/share/keyrings directory. You may encounter this while adding some external repositories like installing Node or Yarn.
Your system will complain about signature verification because of these three reasons:
- While adding an external repository, you missed the step for adding the GPG key and thus you end up with "public key is not available" message and repository is not signed error.
- The developer of the external has started using another key to sign the packages or the previous key is expired and thus you end up with "signatures were invalid: EXPKEYSIG" (Expired Key Sign)
- For some reasons, your distribution's repository or PPA key was changed but not updated on the system. And thus you see 'public key is not available: NO_PUBKEY" message or BADSIG error (Bad/Incorrect Sign)
When you identify the root cause, you can handle the issue accordingly.
Fixing "repository is not signed" error
I have created a sample scenario for you. I added the nodesource repository to install Node.js on Ubuntu but I did not add its GPG key.
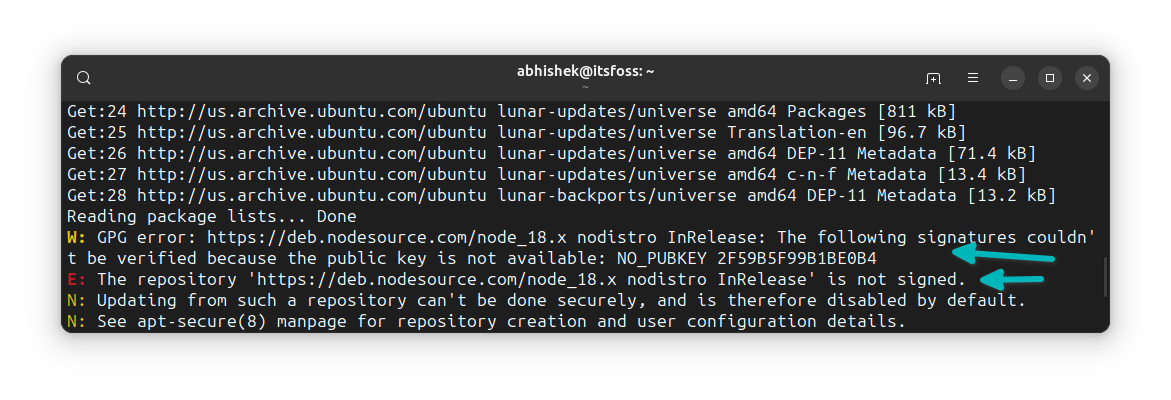
And hence, the system complains that it is expecting the GPG key but cannot find it and hence it cannot verify it. As a result, packages will not be installed from this repository.
The solution here is to add the appropriate GPG key.
How do you do that? Read the error and warning message. Which software and repository it is complaining about. Go to the official website of that software and look for the installation instructions for Debian/Ubuntu. It should have the steps for adding the GPG key.
If you don't find the information on the official website, try to look on other trustworthy websites with similar instructions and tutorials. I mean, you tried to follow the instructions from some tutorial and missed a step. So check the same tutorial.
In my case, the problem was solved when I added the appropriate key (DON'T use it as it is, it's not a generic solution):
sudo mkdir -p /etc/apt/keyrings
curl -fsSL https://deb.nodesource.com/gpgkey/nodesource-repo.gpg.key | sudo gpg --dearmor -o /etc/apt/keyrings/nodesource.gpgFixing "following signatures were invalid: EXPKEYSIG"
In this scenario, you have added an external repository to your Ubuntu system and it was working properly. But lately, either the developer started using a different GPG key or the key expired.
This happened with my DigitalOcean servers I use for quick deployment of Ghost CMS to host It's FOSS and Linux Handbook.
The yarn package was showing:
W: An error occurred during the signature verification. The repository is not updated and the previous index files will be used. GPG error: https://dl.yarnpkg.com/debian stable InRelease: The following signatures were invalid: EXPKEYSIG 23E7166788B63E1E Yarn Packaging [email protected]
W: Failed to fetch https://dl.yarnpkg.com/debian/dists/stable/InRelease The following signatures were invalid: EXPKEYSIG 23E7166788B63E1E Yarn Packaging [email protected]
W: Some index files failed to download. They have been ignored, or old ones used instead.
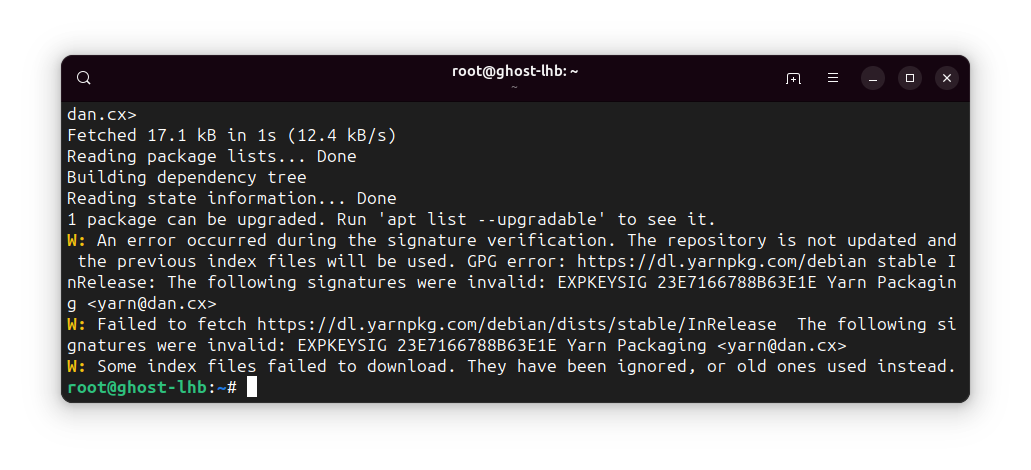
The solution here is to add the new key from the developer. Check the official website for the updated instructions.
Since the trouble was coming from Yarn, I visited the installation page of the Yarn website.
It didn't have a new key explicitly mentioned (like Spotify does). So I repeated the command for adding the GPG key for the Yarn repository.
curl -sS https://dl.yarnpkg.com/debian/pubkey.gpg | sudo apt-key add -
With the new key added to the system, it stopped complaining about the signature verification error.
Fixing "public key is not available: NO_PUBKEY"
This may seem like the first error you saw above but it's not exactly the same.
In that one, the signature key was not added to the system at all. In this one the signature key was added but somehow it is changed or not valid anymore.
W: GPG error: http://repo.mate-desktop.org saucy InRelease: The following signatures couldn’t be verified because the public key is not available: NO_PUBKEY 68980A0EA10B4DE8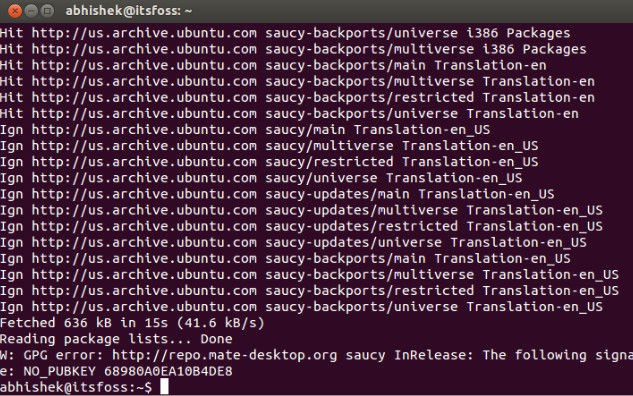
If the issue is coming from an official Ubuntu repository, you may be lucky and get the key from Ubuntu's key servers (this apt-key method will be obsolete in coming years).
Get the key number from the error message displayed on your system. In the above message, the unidentified key is 68980A0EA10B4DE8. It will be something different for you.
Now add this public key to your Ubuntu system using the apt-key command:
sudo apt-key adv --keyserver keyserver.ubuntu.com --recv-keys 68980A0EA10B4DE8If you see a warning message about apt-key command being deprecated, please ignore it.
If the above command adds the key to the system, do a sudo apt update and you should not see this error anymore.
But not everyone is as lucky and hence the next step.
Fixing "following signatures were invalid: BADSIG"
A similar situation where a once working software repository is throwing errors.
In my example, I had Dropbox installed on Ubuntu. It was installed using Deb file that added a repo and key automatically to the system so that newer versions can be available with the system updates.
However, after several months of use, it started showing this error:
W: GPG error: http://linux.dropbox.com/ubuntu kinetic Release: The following signatures were invalid: BADSIG FC918B335044912E Dropbox Automatic Signing Key <[email protected]>
E: The repository 'http://linux.dropbox.com/ubuntu kinetic Release' is not signed.
N: Updating from such a repository can't be done securely, and is therefore disabled by default.
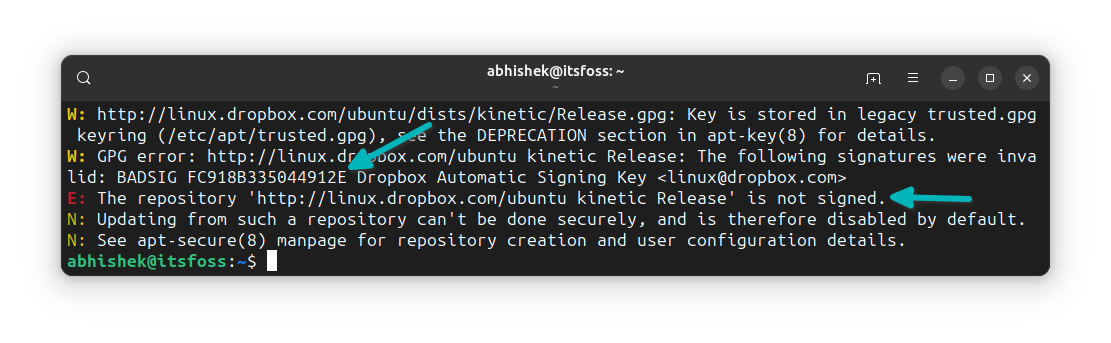
The problem here is that there is no information available on the repository signature key as it was added automatically by the deb file. There is no explicit way to add the key.
The solution here for me was to get the latest deb file once again and run it. It opens the software center and prompts you to remove the installed version first. Uninstall it.
And then run the deb file again. This time, it will install the new version from the deb file.
Did you manage to fix the issue?
I hope you not only fixed the “The following signatures couldn’t be verified” error, you also know why it happened and how it was fixed.
As I mentioned earlier, it's not 'run this command to fix this issue' kind of problem. You have to identify the root cause and then try to follow the suggestions. That leaves quite some work on your end but that's what it is.
🗨 Now your turn. Did you manage to fix the problem? Which issues was that? Do you still need help? The comment section is all yours.

