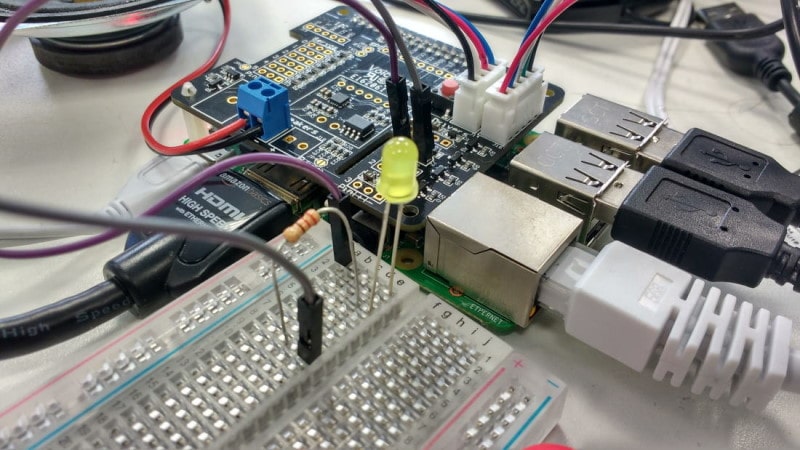
It won’t be an exaggeration to call Raspberry Pi a revolutionary gadget. When it was first launched in 2011-12, people couldn’t believe that a computer could be available for just $25 🤯
If you bought a Pi and wondering, what you should do with Raspberry Pi, we have some ideas. I will list some cool Raspberry Pi projects you can start following in your free time.
These Raspberry Pi project ideas are not limited to Pi. You can use them with other Raspberry Pi like devices such as Orange Pi, Khadas, etc.
36 Cool Raspberry Pi Projects
I have listed several of these project ideas by categorizing them in terms of the level of complexity (beginner, intermediate, and advanced). Some projects need additional equipment and sensors as well.
👶 Beginner-Level Raspberry Pi Projects
Of course, it is worth noting that it will be subjective to what expertise you have. We assume the projects with less configuration and prerequisites as fit for beginners.
1. Media Server
Building a media server using Raspberry Pi is the most common and probably the easiest project.
You can take a look at some of the best media server software available for Linux and get started.
To know more about it, you can refer to the official documentation of using Kodi with Raspberry Pi (one of the available media server software).
2. Weather Station
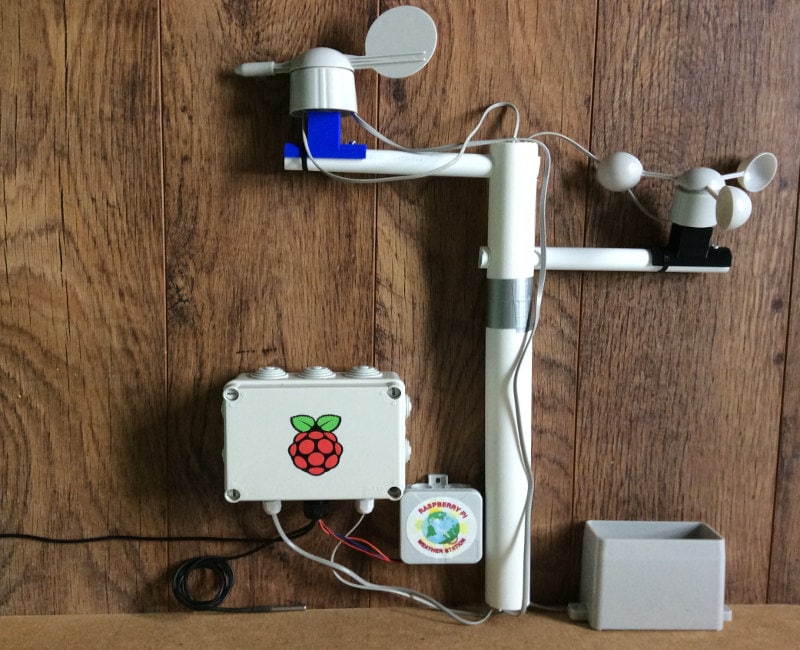
Building a weather station using Raspberry Pi should be fun if you’re good at building projects with electronic components.
This may not be the easiest one to start with – but it’s quite simple if you carefully look into the project requirements.
You will be able to collect weather data using a variety of sensors as per your requirements. The project has been listed on the official website to help you build it as easy as possible.
3. The Parent Detector
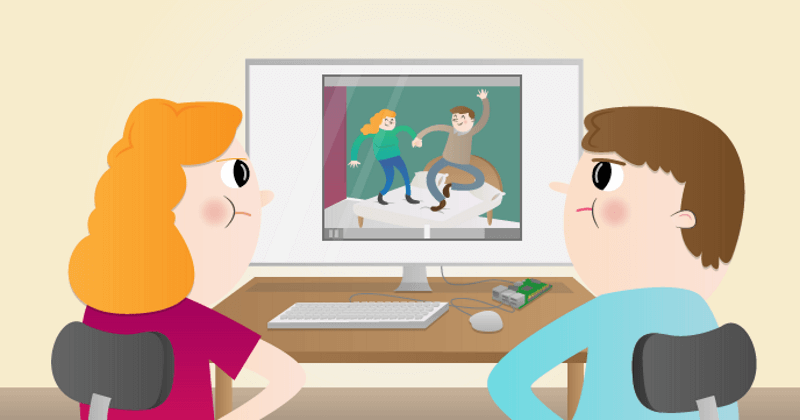
Yet another project from Raspberry Pi’s official website, this project uses minimal hardware to set up a motion detector which then triggers a video recording using the Raspberry Pi camera module.
The use-case for this can be a lot of things. If you are a parent, you can watch your child when they enter their room. In either case, this can also be handy to keep an eye on your door as a security measure to check when someone arrives.
You can find all the necessary details on Raspberry Pi’s official site.

Pironman 5 Case With Tower Cooler and Fan
This dope Raspberry Pi 5 case has a tower cooler and dual RGB fans to keep the device cool. It also extends your Pi 5 with M.2 SSD slot and 2 standard HDMI ports.
4. FM Radio Station
Raspberry Pi is an inexpensive device for making an FM radio station. The prerequisites may not be much but they are worth exploring for fun.
Note that you may not want to interfere with the local FM frequencies. You can find all the details to set it up by clicking the button below.
5. Minecraft Game Sever

Minecraft is quite a popular game. However, you might have to pay a premium if you want a personal server.
Fret not; you can use your Raspberry Pi to build a local server, create your world and have fun with your family/friends.
6. Temperature Log
I found something interesting on the official Raspberry Pi website to help you learn a few things, like how to write data to a file etc.
Here, you will be recording the temperature using the sensor present.
For this, you will be utilizing the command line to monitor the temperature of Raspberry Pi.
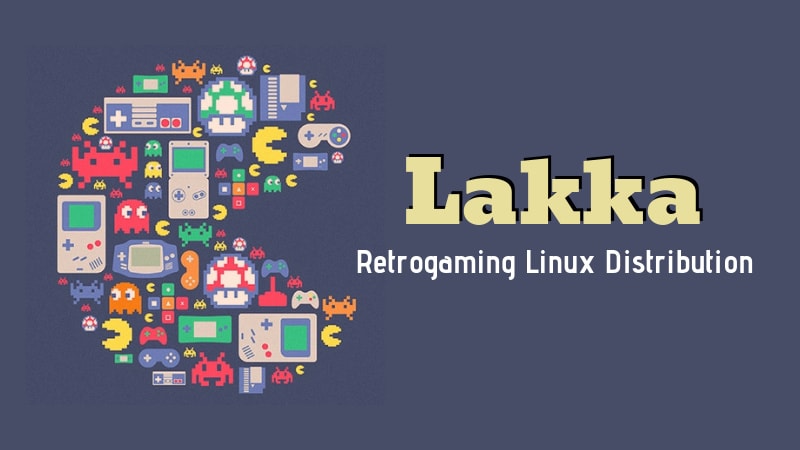
7. Retro Gaming Console
You can turn your Raspberry Pi into a gaming console by simply installing an OS on an SD card and transferring a few files.
I have linked a resource to help you do this project in the button below.
Suggested Read 📖
8. Full-Fledged Desktop

If you would instead not invest a lot to build a PC, you can easily utilize your Raspberry Pi to build one.
Technically, your Raspberry Pi will be the heart of your PC, and you will need to add accessories (monitor, keyboard, mouse, etc.) to turn it into a PC. You can also build a custom case for the board, which is optional.
The PC won’t be powerful enough for all kinds of tasks—but it will be usable. You can also check out the experience of having Raspberry Pi 4 as a desktop replacement on their official website as a reference to this project.
9. Self Host Bitwarden

Bitwarden is one of the best open-source password managers. This cool Raspberry Pi project helps you to set up your self-hosted Bitwarden instance.
Add another layer of protection for your accounts. Take a look at the detailed project through the link below.
10. Run Xbox Cloud Gaming

This project lets you utilize Xbox cloud gaming on your Raspberry Pi. This project will even walk you through the steps of turning your Raspberry Pi into a pure Xbox Cloud Gaming machine with the “lite” flavor of the operating system.
You can explore more about it in the link below.
11. Internet Speed Monitor
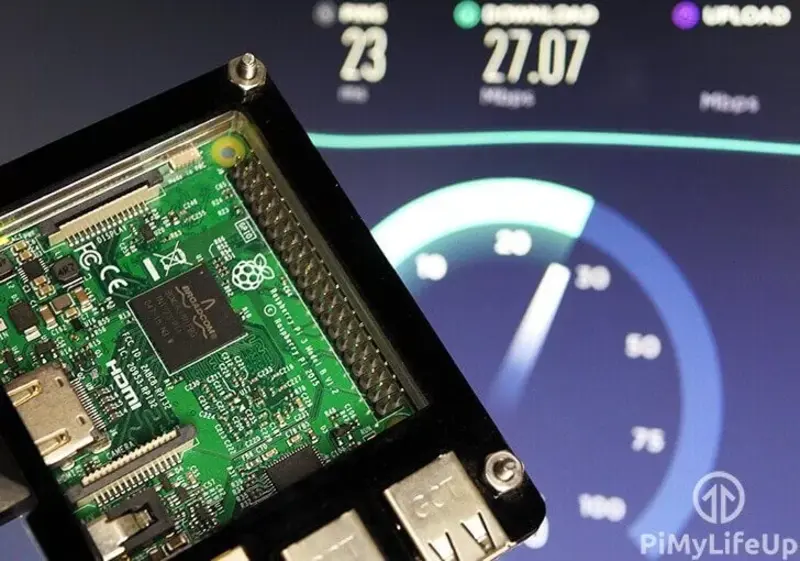
You can use your Raspberry Pi to monitor your internet connection and save the data to view in Grafana or Google Drive.
12. Wi-Fi Bridge
This is yet another beginner-level project where you can convert your Raspberry Pi into a Wi-Fi Bridge. This is one of the best ways of providing internet access to a device that only supports an Ethernet connection.
13. Internet Radio and Streaming
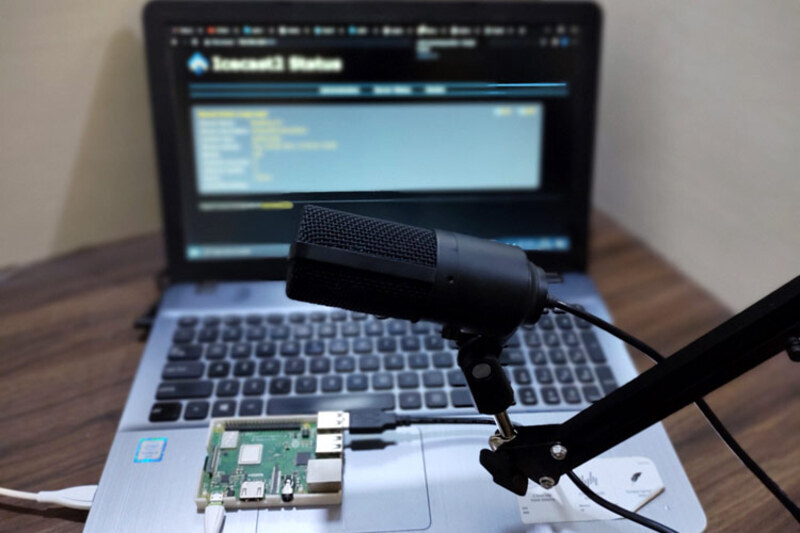
Set up a Raspberry Pi streaming station using DarkIce and Icecast, the two Raspberry Pi packages used for audio recording, encoding, and streaming. You may need a Pi and a Microphone to try this one. Check the detailed guide from the button below.
14. Meeting Indicator

Working from home has been a trend since the pandemic started. There are possibilities for disturbances when you are working from home. This Raspberry Pi is both a fun and useful project. Let others know that you are busy.
🤓 Intermediate-Level Raspberry Pi Project Ideas
15. Build a LAMP Web Server with WordPress
If you are into web development, you can try setting up a LAMP (Linux + Apache + MySQL + PHP) server and install WordPress to create a website. You can also choose to make something else from scratch without installing WordPress.
You can access the site on any device on the same network as your Raspberry Pi.
16. Laser Tripwire
It is a similar concept to the parent detector that uses a motion sensor. In this case, a laser beam is used to detect activity whenever someone breaks the beam.
You need a few things to set up the alarm and complete the tripwire. Of course, this is a simple project to start with that has potentially different applications.
17. Print Server
What if you can turn your old printer to work on a network of devices without requiring a built-in WiFi feature?
Well, that’s what this project is about. You can access your printer from multiple devices using a print server. Check out all the details to help build one by clicking the button below.
18. Time Lapse Camera
Looking for a cheap dedicated time-lapse camera? Well, you can do it yourself with a Raspberry Pi.
You can use the Pi camera module or explore other options as well.
19. Music Box
You can build a button-controlled music box using Raspberry Pi to have a great time with your kids or anyone who loves music.
When you press a button, it will play a sound. You can find the short project description in the video above; click on the button below for more details.
20. Google Home On Raspberry Pi
If you could configure and set up Google Assistant on your Raspberry Pi, you can turn it into an inexpensive Google Home DIY alternative.
Fortunately, you can achieve that with your Raspberry Pi. Find out more about it in the video above.
21. Build a Smart TV Box
If you know how to set up a media server on Raspberry Pi (as mentioned in the first project idea of this article), you can make this happen too.
With the help of the Kodi box (or similar), you can build your smart TV box powered by the media server of your choice.
22. Add Gesture Controls To Raspberry Pi
You can add the ability to have gesture controls for any of your projects on Raspberry Pi using a Flick board.
It may not be the cheapest project, but it is an impressive touch for your Raspberry Pi project.
23. DNS server
This project benefits tinkerers and those who want private and secure internet. A private DNS powered by Raspberry Pi can cater to both types of enthusiasts. You can find the detailed project through the button below.
Suggested Read 📖
24. Raspberry Pi Powered Bonsai Watering

Take care of your Bonsai trees with this project. You do need a few extra things to make it work, but it should be a fun and informative project. Take a look at the detailed project from here.
25. Air Quality Monitoring
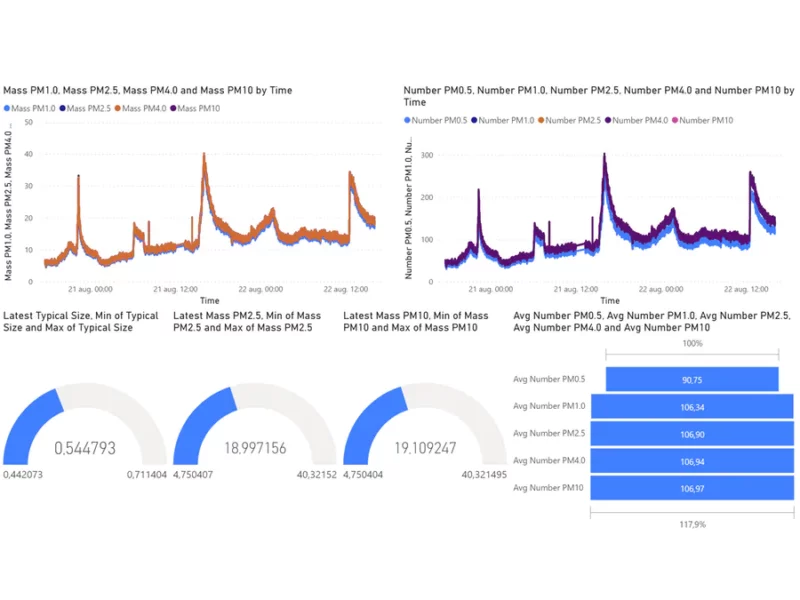
Air quality is a more pressing issue nowadays with the climate change and pollution. With Raspberry Pi and a particulate matter sensor, your DIY air quality monitoring tool can be used.
26. Wire Loop Game
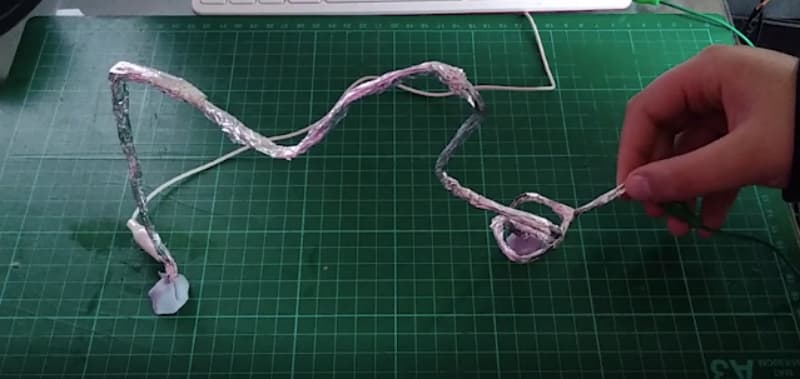
Are you interested in the classic wire loop game? This project describes how to set up a simple wire-loop game, using your Raspberry Pi and some additional equipment. Check the detailed guide from the official Raspberry Pi projects link down below.
27. RFID Attendence System
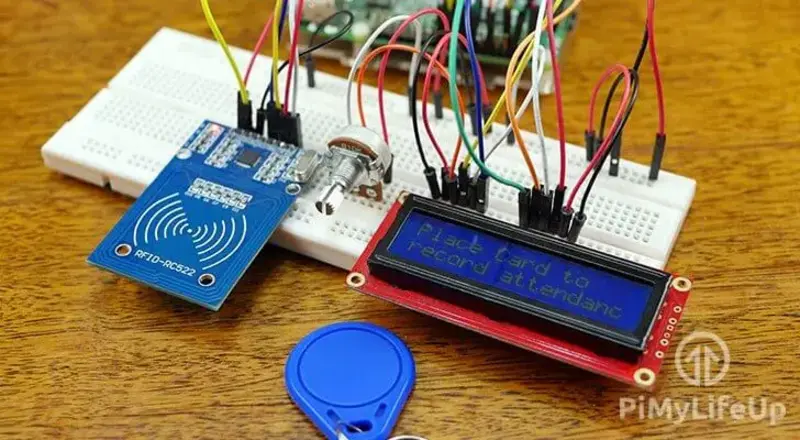
RFID-based projects were cool hobby projects during my college days. A pretty cool project if you ask me!
👨💻 Advanced Level Raspberry Pi Project Ideas
28. Tor Router
If you want to explore ways to enhance your digital privacy, you can start by building your own local Tor onion router.
With this, you can scramble your Internet connection and remain anonymous with your browsing activities. It is just something like a VPN, but technically different.
29. Control LEDs with your voice
This is quite interesting. I have already mentioned a project where you can set up Google Assistant on your Raspberry Pi. However, in this case, you can control the LEDs with your voice.
You will not need the assistant this time, all you need is the Google AIY voice kit. This has been featured on the list of official DIY projects using Raspberry Pi, you can get more information there.
30. Wi-Fi Extender
If you want to increase the range of your Wi-Fi network, you might have to opt for a premium gadget to help you do that, or you can utilize Raspberry Pi to get the job done.
Yes, that’s right, you can build a Wi-Fi extender by just using your Raspberry Pi.
31. VPN Server
You do not need to trust the VPN providers if you can build your local VPN server. It can be quite challenging to make it happen.
So, if you are up for some action, you can use your Raspberry Pi to make a private VPN server for your connection. Explore more about it here:
32. Home Automation Using Raspberry Pi
A lot of powerful projects can be done using Raspberry Pi, one of which is – ‘Home Automation’.
If I want to implement home automation, it will be expensive. But, if I use Raspberry Pi to create something similar, it will require less investment. Of course, you will have to explore and improve to make it a reliable system but you can get started with the basics.
33. Local Cloud Server
You can also build your cloud using Raspberry Pi. You can also install Nextcloud on it to protect and store your data.
Numerous exciting things to explore once you have your cloud, right?
34. Portable Hacking Device
Let me make one thing clear; I am not encouraging you to do something illegal (just like the movies) by building a portable hacking device.
So, just for educational/testing purposes, feel free to try making your own portable device for hacking using Raspberry Pi.
35. Smart Gloves
Making a pair of smart gloves is a cool project with Raspberry Pi. In my college days, I witnessed a senior do this thing; it was interesting.
You can refer to the official resource for this project and get started.
36. Ad Blocker
With Raspberry Pi, you can easily implement a network-wide Ad blocker so that you won’t have to install ad blockers separately on devices or browsers.
You need to utilize Pi-Hole (the ad blocker) to set it up. We have a guide on that to help you out as well:
More project ideas for Raspberry Pi enthusiasts
Here, I list some of the most intriguing projects I could find that might be helpful. Some of these projects can be created with cheaper and smaller Raspberry Pi Zero like devices as well.
We have a dedicated list of Raspberry Pi Zero W projects to explore, if you are curious.
Some project examples for Raspberry Pi Pico:

And if you have got it already, here are a few project ideas for Raspberry Pi AI camera:
💬 If you know of other superb ideas, please let me know in the comments below. I might update this list of Raspberry Pi projects with your idea.





