I usually don’t encrypt files – but if I am planning to organize my important documents or credentials, an encryption program would come in handy.
You may be already using a program like GnuPG that helps you encrypt/decrypt your files on your Linux machine. There is EncryptPad as well that encrypts your notes.
However, I have come across a new free encryption tool called FinalCrypt. The software is licensed with CC BY-NC-ND which is enote entirely compatible with the definition of open source.
You can check out their recent releases and the source on its GitHub page.
In this article, I will be sharing my experience of using this tool. Do note that I won’t be comparing this with any other program available out there – so if you want a detailed comparison between multiple solutions, let us know in the comments.
Using FinalCrypt to encrypt files
FinalCrypt uses the One-Time pad key generation cipher to encrypt files. In other words, it generates an OTP key which you will use for encrypting or decrypting your files.
The key will be completely random as per the size of the key – which you can specify. So, it is impossible to decrypt the file without the key file.
While the OTP key method for encryption/decryption is simple and effective, but managing or securing the key file could be an inconvenience for some.
If you want to use FinalCrypt, you can install the DEB/RPM files from its website. FinalCrypt is also available for Windows and macOS.
Once downloaded, simply double click to install it from deb or rpm files. You can also build it from the source code if you want.
FileCrypt in Action
This video shows how to use FinalCrypt:
If you like Linux related videos, please subscribe to our YouTube channel.
Once you have installed FinalCrypt, you’ll find it in your list of installed applications. Launch it from there.
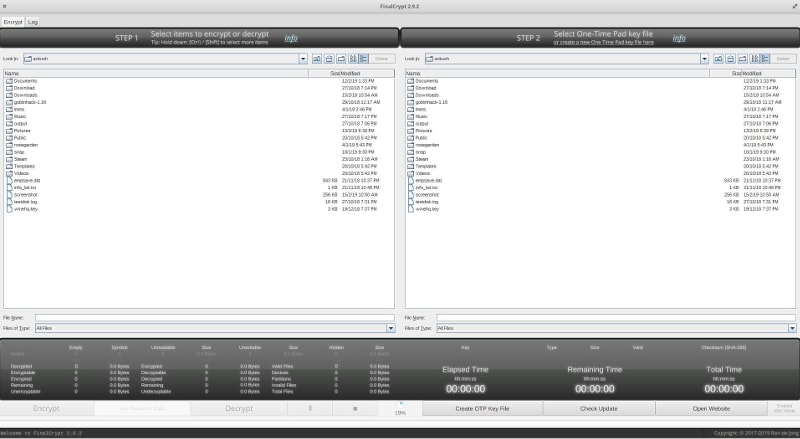
Upon launch, you will observe two sections (split) for the items to encrypt/decrypt and the other to select the OTP file.
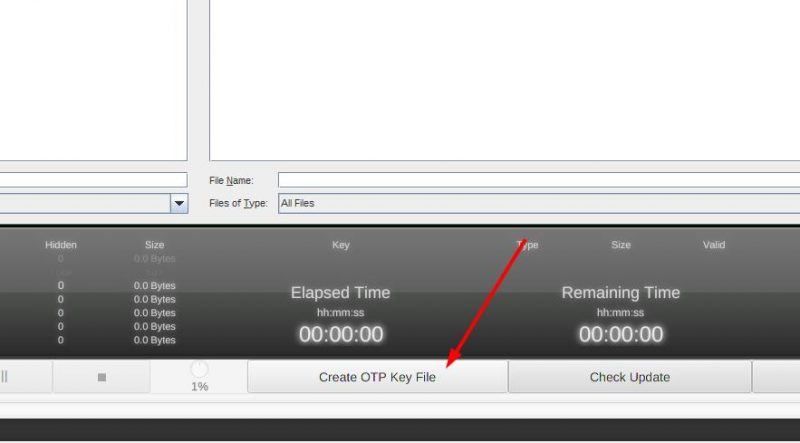
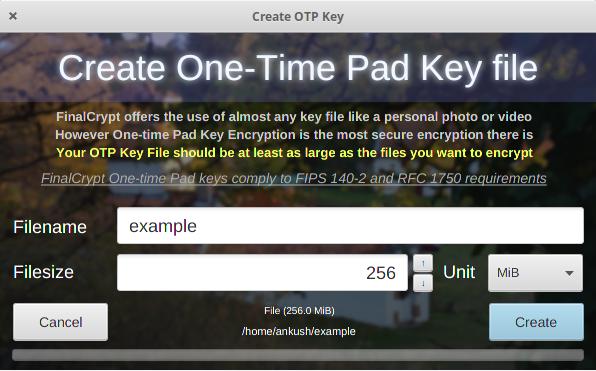
First, you will have to generate an OTP key. Here’s how to do that:
Do note that your file name can be anything – but you need to make sure that the key file size is greater or equal to the file you want to encrypt. I found it weird but that’s how the One-time pad encryption works.
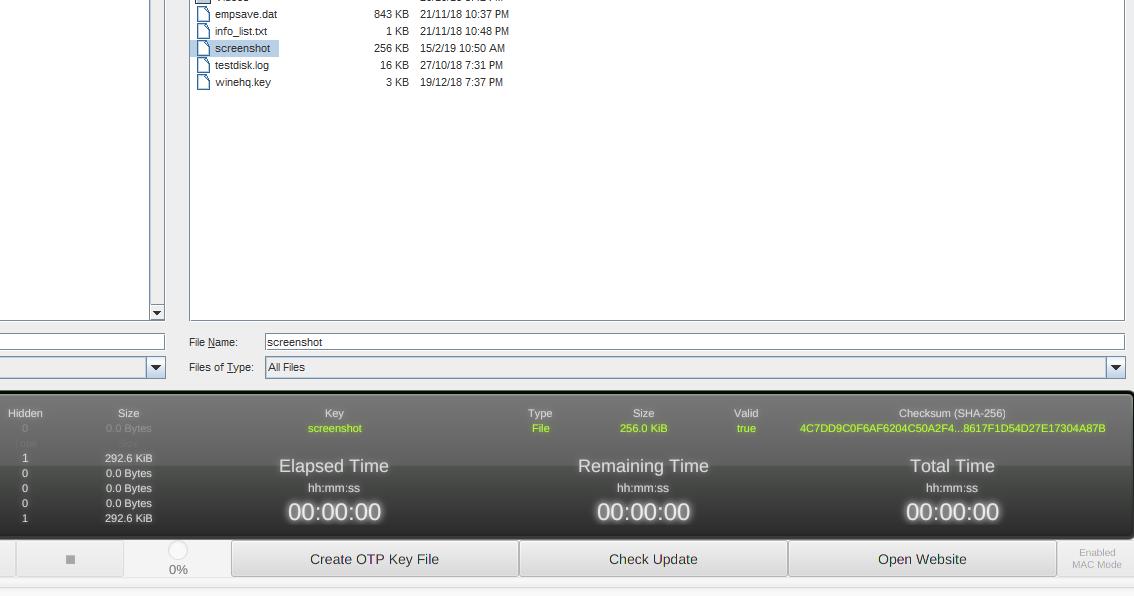
After you generate the file, select the key on the right-side of the window and then select the files that you want to encrypt on the left-side of the window.
You will find the checksum value, key file size, and valid status highlighted after generating the OTP:
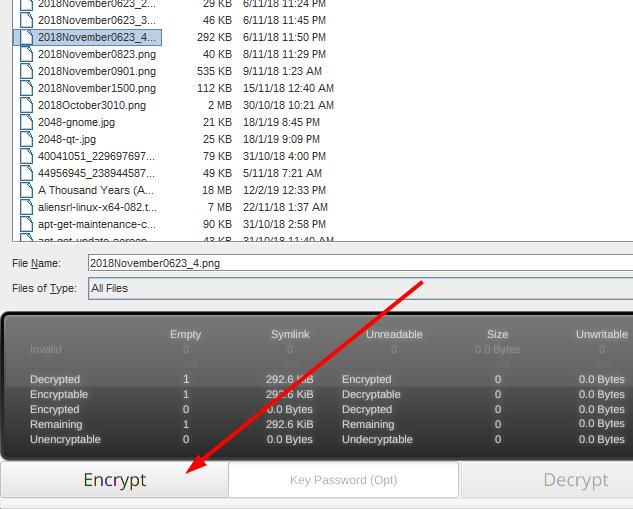
After making the selection, you just need to click on “Encrypt” to encrypt those files and if already encrypted, then “Decrypt” to decrypt those.
You can also use FinalCrypt in command line to automate your encryption job.
How do you secure your OTP key?
It is easy to encrypt/decrypt the files you want to protect. But, where should you keep your OTP key?
It is literally useless if you fail to keep your OTP key in a safe storage location.
Well, one of the best ways would be to use a USB stick specifically for the keys you want to store. Just plug it in when you want to decrypt files and its all good.
In addition to that, you may save your key on a cloud service, if you consider it secure enough.
More information about FinalCrypt can be found on its website.
Wrapping Up
It might seem a little overwhelming at the beginning but it is actually a simple and user-friendly encryption program available for Linux. There are other programs to password protect folders as well if you are interested in some additional reading.
What do you think about FinalCrypt? Do you happen to know about something similar which is potentially better? Let us know in the comments and we shall take a look at them!

